Trustwave Log Management Appliances
Designed for businesses that need an easy-to-implement log collection and management solution
Information contained in logs provides critical visibility into events and incidents within your environment. Reviewing these logs and setting up automated notifications are essential in providing security and compliance benefits, enabling forensic investigations and system administration, and helping organizations achieve their overall business objectives. Trustwave Log Management Appliances are designed to collect and process logs, and make sense of all the available data.
Overview:
Part of our SIEM portfolio, Trustwave Log Management Appliances consist of Log Management Enterprise (LME) and Log Collector (LC) appliances.
They are designed for organizations that need an easy-to-implement log collection and management solution to serve either as a standalone solution, part of a larger SIEM solution or part of a Trustwave Managed Security Services solution. With Trustwave products, no additional storage, licensing, or compliance packages are needed – which means you can accurately predict costs.
Why do customers choose Trustwave Log Management Appliances?
- Audit-ready reporting on compliance objectives.
- Near real-time access to security events and logs.
- Powerful correlation and notifications with more than 70 configurable templates.
- Granular permissions support organizational roles.
- Turnkey appliance requires no other infrastructure.
Features:
Log Management Enterprise
Collecting and processing logs, and making sense of all the available data, can be challenging. As an appliance-based solution that is easy to deploy, operate, manage and use, Trustwave Log Management Enterprise (LME) helps simplify these challenges.
Trustwave LME includes support for hundreds of auditing devices from a myriad of vendors and offers a primarily agent-less approach, which simplifies ongoing operational maintenance requirements and reduces total cost of ownership.
Using embedded real-world expertise, LME identifies important audit and security events in real time. In addition, it offers:

Analytics
- Powerful visual filtering capabilities help conduct pre-incident analysis through optimized search of the self-contained Security Data Warehouse™ (SDW) log repository.
- LME's Event Explorer can be used for troubleshooting, user-activity tracking and forensic investigation, as well as visual analysis.
- The add-on Trustwave Threat Correlation Services provides additional insight into known attackers and threats to provide a heightened level of situational awareness, enabling organizations to leverage intelligence derived from Trustwave's research to improve their security posture.

Anywhere Log Management
- Deployments range from a single appliance to a hierarchical implementation of multiple appliances, aligned with remote geographic sites or to meet separation of data requirements.
- Logs accepted directly from almost any source or from other Trustwave Log Management appliances.
- Centralized logging plus event management with SDW, when more than one appliance is deployed.

Compliance Support
- Indicators of compliance and policy violations, network health issues and security threats are hidden in terabytes of log data. LME empowers your discovery, remediation and compliance.
- Satisfies the log management mandate of industry requirements, regulations and standards, including HIPAA, PCI DSS, FISMA, GLBA, COBIT, ISO 27002, NERC CIP and GPG 13.
Log Collector
This product collects, compresses, encrypts, and forwards logs from one location to an upstream SIEM product portfolio component for further processing, analysis and correlation.
How It Works:
Trustwave Log Management Appliances at a Glance
The Event Explorer feature offers granular search capabilities.
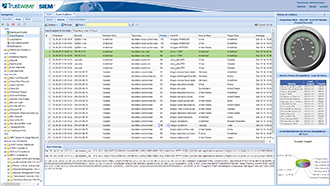
Event Explorer can be used for troubleshooting, tracking user activity and investigating forensics, as well as visual analysis.
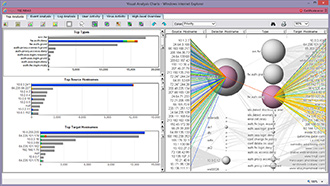
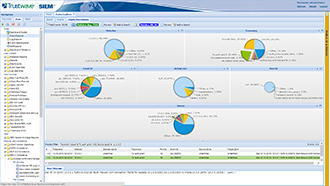
Visually compelling charts provide a simple and intuitive way to analyze log data and take action.
Specifications:
| LME 2-10 | LME 2-20 | LME 2 | LME 3 | LME 4 | LME 5 | |
|---|---|---|---|---|---|---|
| EPS* | 115 | 230 | 460 | 925 | 1735 | 3400 |
| EPD* | 10 million | 20 million | 40 million | 80 million | 150 million | 300 million |
| RAM | 12 GB | 12 GB | 12 GB | 16 GB | 24 GB | 48 GB |
| Effective Storage** | 9 TB | 9 TB | 9 TB | 18 TB | 29 TB | 44 TB |
| Online Retention*** | 5 years | 4 years | 3 years | 3 years | 2 years | 1 year |
| Redundant Power | ||||||
| Interfaces | 4 GIG Eth | 4 GIG Eth | 4 GIG Eth | 4 GIG Eth | 4 GIG Eth | 4 GIG Eth |
Documentation:
Download the Trustwave Log Management Enterprise Datasheet (PDF).
Download the Trustwave SIEM Datasheet (PDF).
